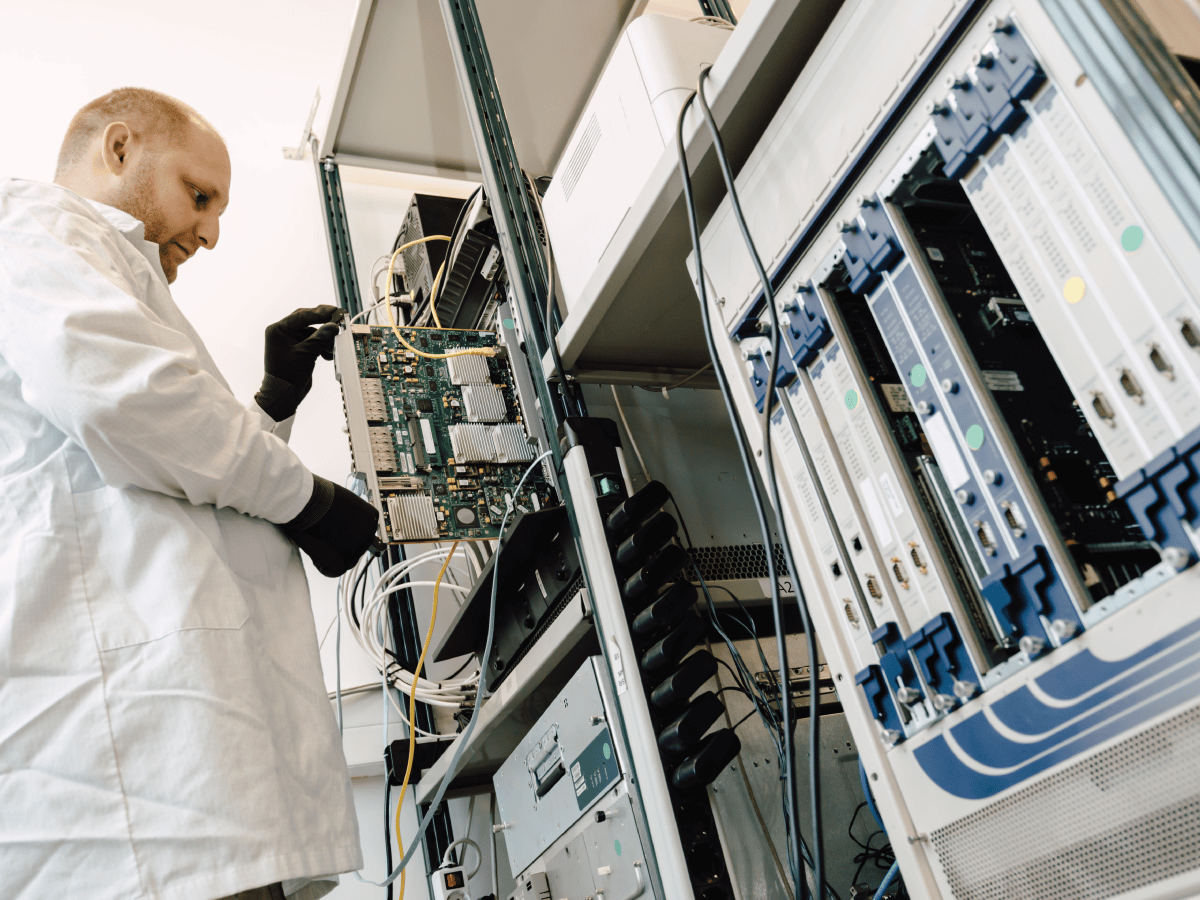
Organizations need a secure infrastructure that supports all aspects of their operations including network security services with process automation, policy management for users and devices, IoT connection, and application security for collaboration and communication tools. The challenge is lowering the hazards brought on by cloud computing, shadow IT, Internet of Things (IoT), and bring your own device (BYOD) policies.
Our network security engineers provide 24/7 threat hunting, detection, and response as a fully managed solution.